A recent vRealize Automation Cloud (vRAC) use case involved applying AWS Security Groups(SG) when deploying a new machine. First, every new AWS machine will be assigned two standard SGs. A third one will be assigned based on the application type (Web, App, DB).
After looking at the Cloud Assembly blueprint expression syntax page, it looked like we would be limited to only two options in our condition (if else). For example, ${input.count < 2 ? "small" : "large"}. Or if input.count < 2 then “small” else “large”.
But we have three options, not two. Effectively we needed.
if (extraSG == 'web' {
then web_sg }
else if (extraSG = 'app' {
then app_sg }
else {
db_sg
}
Or using javascript shorthand.
extraSG == 'web' ? web_sg : extraSG == 'app' ? app_sg : db_sg
Or converted into something vRAC can consume.
${input.extraSG == "web" ? resource.WEB_SG.id : input.extraSG == "app" ? resource.APP_SG.id : resource.DB_SG.id}
Lets see what happens when we deploy this blueprint selecting WEB_SG from the list.
formatVersion: 1
inputs:
extraSG:
type: string
title: Select extra SG
default: web
oneOf:
- title: WEB_SG
const: web
- title: APP_SG
const: app
- title: DB_SG
const: db
resources:
WEB_SG:
type: Cloud.SecurityGroup
properties:
name: WEB_SG
constraints:
- tag: 'nsx:compute_web_sg'
securityGroupType: existing
APP_SG:
type: Cloud.SecurityGroup
properties:
name: APP_SG
constraints:
- tag: 'nsx:compute_app_db'
securityGroupType: existing
DB_SG:
type: Cloud.SecurityGroup
properties:
name: DB_SG
constraints:
- tag: 'nsx:compute_db_sg'
securityGroupType: existing
vmOverlay:
type: Cloud.SecurityGroup
properties:
name: NSX Overlay
constraints:
- tag: 'nsx:vm-overlay-sg'
securityGroupType: existing
WebDMZ:
type: Cloud.SecurityGroup
properties:
name: WebDMZ
constraints:
- tag: 'nsx:compute_webdmz'
securityGroupType: existing
Cloud_Machine_1:
type: Cloud.Machine
properties:
remoteAccess:
authentication: keyPairName
keyPair: id-rsa
image: RHEL 8
flavor: generic.small
constraints:
- tag: 'cloud_type:public'
tags:
- key: nsxcloud
value: trans_ssh
networks:
- network: '${resource.Cloud_Network_1.id}'
assignPublicIpAddress: false
securityGroups:
- '${resource.WebDMZ.id}'
# Adding for NSX Cloud
- '${resource.vmOverlay.id}'
# if input.extraSG = "web" then WEB_SG else if imput.extraSG = "app" then APP_DB else DB_SG
- '${input.extraSG == "web" ? resource.WEB_SG.id : input.extraSG == "app" ? resource.APP_SG.id : resource.DB_SG.id}'
Cloud_Network_1:
type: Cloud.Network
properties:
networkType: existing
constraints:
- tag: 'nsx:cloud_compute'
Let’s take a look at the deployment topology from vRAC.
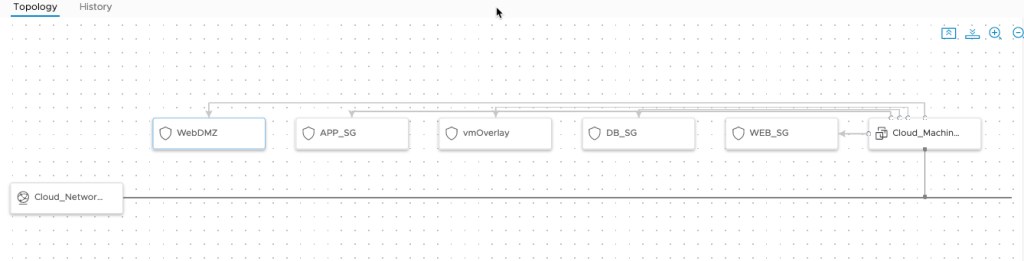
This diagram indicates that all of the SGs where attached to the machine. That can’t be right. I wonder what the machine looks like in AWS.

Hmm, looks like a bug to me.
Now on to leveraging NSX Cloud with vRAC. Stay tuned.
One thought on “vRAC Security Groups lessons learned”