This is follow up to the previous article. A co-worker of mine came up with a better and much cleaner solution.
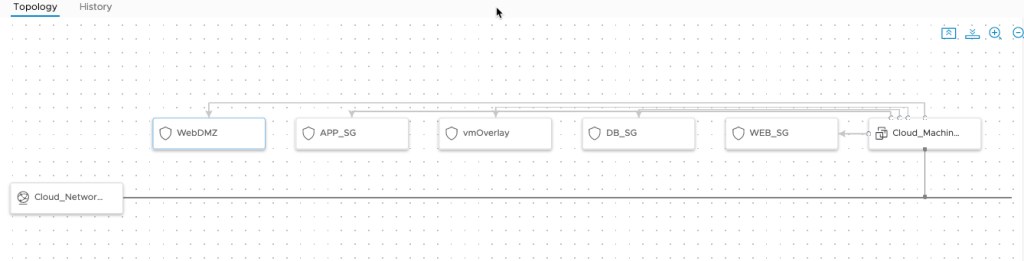
My original solution worked, but introduced a nasty deployment topology diagram. In effect it showed every SG as attached, even unused ones. This diagram is very misleading and doesn’t reflect the actual assignment of the Security Groups.
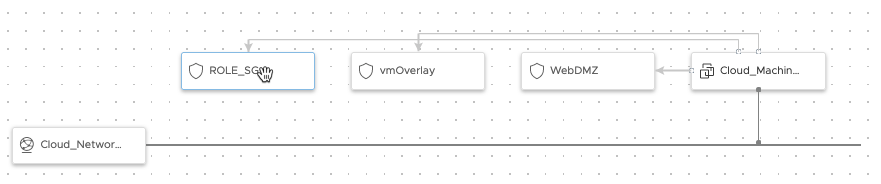
The new solution is much cleaner and more closely represents what the user actually requested. Here the two mandatory SG’s as well as the required role SG are attached.
The new conceptual code seemed logical, but vRAC just didn’t like it.
formatVersion: 1
inputs:
extraSG:
type: string
title: Select extra SG
default: nsx:compute_web_sg
oneOf:
- title: web
const: nsx:compute_web_sg
- title: app
const: nsx:compute_app_sg
- title: db
const: nsx:compute_db_sg
resources:
ROLE_SG:
type: Cloud.SecurityGroup
properties:
constraints:
- tag: '${input.extraSG}'
securityGroupType: existing
Cloud_Machine_1:
type: Cloud.Machine
properties:
image: RHEL 8 - Encrypted EBS
flavor: generic.small
networks:
- network: '${resource.Cloud_Network_1.id}'
assignPublicIpAddress: false
securityGroups:
- '${resource.ROLE_SG.id}'
After some tinkering I came up the following blueprint.
formatVersion: 1
inputs:
nsxNetwork:
type: string
default: compute
enum:
- compute
- transit
extraSG:
type: string
title: Select extra SG
default: web
enum:
- web
- app
- db
resources:
ROLE_SG:
type: Cloud.SecurityGroup
properties:
name: '${input.extraSG + ''_sg''}'
constraints:
- tag: '${''nsx:'' + input.nsxNetwork + ''_'' + input.extraSG + ''_sg''}'
securityGroupType: existing
vmOverlay:
type: Cloud.SecurityGroup
properties:
name: NSX Overlay
constraints:
- tag: 'nsx:vm-overlay-sg'
securityGroupType: existing
WebDMZ:
type: Cloud.SecurityGroup
properties:
name: WebDMZ
constraints:
- tag: 'nsx:compute_webdmz'
securityGroupType: existing
Cloud_Machine_1:
type: Cloud.Machine
properties:
remoteAccess:
authentication: keyPairName
keyPair: id-rsa
image: RHEL 8 - Encrypted EBS
flavor: generic.small
constraints:
- tag: 'cloud_type:public'
tags:
- key: nsxcloud
value: trans_ssh
networks:
- network: '${resource.Cloud_Network_1.id}'
assignPublicIpAddress: false
securityGroups:
- '${resource.WebDMZ.id}'
# Adding for NSX Cloud
- '${resource.vmOverlay.id}'
# if input.extraSG = "web" then WEB_SG else if imput.extraSG = "app" then APP_DB else DB_SG
# - '${input.extraSG == "web" ? resource.WEB_SG.id : input.extraSG == "app" ? resource.APP_SG.id : resource.DB_SG.id}'
- '${resource.ROLE_SG.id}'
Cloud_Network_1:
type: Cloud.Network
properties:
networkType: existing
constraints:
- tag: 'nsx:cloud_compute'
As you can see, there is more than one way to solve use cases with vRAC. The key sometimes is just to keep trying different options to get the results you want.